A cyberattack can be extremely profitable, and it's a business that never sleeps. In fact, according to a study by Maryland University, a cyberattack occurs approximately once every 39 seconds.
SaaS tools and environments are especially attractive to cybercriminals due to their rising popularity among businesses. These applications store a lot of sensible and important data. So nowadays, companies face several data security challenges.
SaaS security challenges can be quite unique in their nature. But don’t worry, we’ve got you covered.
By entering your email you agree to the Privacy Policy and consent to receive emails from Cledara.
What Is SaaS Security?**
In essence, SaaS security is a set of practices, protocols, and processes that have the primary goal of ensuring the security of a company's software stack.
The responsibility for implementing these practices extends beyond the SaaS provider alone. SaaS security involves multiple stakeholders, including:
- The vendor
- The client
- The cloud provider
When a cyberattack occurs, the consequences are shared, and each stakeholder is affected in different ways.
According to the official (ISC)² guide to the CCSP CBK:
Moreover, SaaS security is primarily managed by IT teams within companies, but it is a shared responsibility throughout the organization.
SaaS Security Risks
When discussing software security risks, it is widely acknowledged that they have detrimental effects. However, it is important to understand the specific consequences a cyberattack can bring to your company, some of them include:
- Data breaches
- Financial losses
- Reputational damage
- Productivity decline
- Business continuity issues
What Puts Your Company at Risk?**
There are many security risks in the SaaS landscape, but let's look at the most common and relevant ones:
- Shadow IT
- Misconfigurations
- Access management
- Compliance issues
- Supply chain vulnerabilities
Let's take a closer look.
Shadow IT
Shadow IT refers to the use of software without proper authorization, management, or support from the IT team or other relevant stakeholders.
Some of the most common cases of informal SaaS include:
- Project management tools that team members use for their personal projects
- Internal communication tools that are used within a small team
- Process documentation tools that are adopted ad-hoc
While these cases may seem harmless, the truth is that any tool has the potential to become shadow IT. According to a recent study of 200 companies, 65% of all SaaS apps are Shadow IT.
Unsafe software can become a security concern if it interacts with critical company data, and lead to:
- Unauthorized access and changes to data
- Introduction of malicious code
- Compliance issues
- Significant financial losses
Misconfigurations
SaaS products typically offer multiple layers of configuration that users must set up based on their security and privacy policies. Misconfigurations in privacy settings can present significant vulnerabilities for companies. For instance, neglecting to configure multi-factor authentication (MFA) or granting excessive data access to users can result in a cascade of cyberattacks and data breaches.
Access Management
When it comes to SaaS security, limiting user profiles' access is also crucial. This entails keeping rigorous control over which profiles are granted access to SaaS tools, the number of profiles with access, and the privileges they have.
Imagine that an employee leaves the company and no one revokes their access to the company's tools. Or if a junior employee has permission to make critical changes in a tool’s database. It could lead to a security catastrophe.
Compliance Issues
Some SaaS providers don’t comply with industry-specific regulations, which can heighten the risk of data breaches or loss. Besides, it can also lead to legal penalties, financial losses, and even damage your company’s reputation.
For instance, if an online store works with a SaaS tool that doesn’t comply with Payment Card Industry Data Security Standard (PCI DSS) requirements, it can lead to the loss of customer data and financial setbacks.
Therefore, you should carefully assess the regulatory compliance features and practices of any SaaS provider you consider using.
Here are a few examples of compliance requirements based on different industries:
Supply Chain Vulnerabilities
Every piece of software, including SaaS tools, consists of various components that may occasionally be beyond your control. Vulnerabilities in the supply chain can lead to serious security problems. In fact, this was the cause of one of the biggest cyber-attacks in recent times.
Plus, oftentimes SaaS providers integrate with third-party applications, such as payment processors or marketing platforms. This can also heighten the risk of security incidents, since vulnerabilities in third-party software could impact the entire system.
Controlling the entire supply chain can be a challenging task. However, more procedures are being implemented to fully understand it and manage its components. SBOMs are a clear example.
10 SaaS Security Best Practices**
As we saw, SaaS security is a challenge. Fortunately, there are multiple best practices that your company can adopt to enhance its SaaS security. We recommend that you:
- Enhance processes to avoid shadow IT
- Control your onboarding & offboarding processes
- Choose the right vendor
- Design a recovery plan
- Implement identity and access management
- Prefer SASE products
- Use encryption
- Train your staff
- Automate operations
- Apply Zero Trust policies
Establish Processes to Avoid Shadow IT
Contrary to popular belief, shadow IT is often unintentional. Many employees sign up for tools just to streamline their processes.
They usually overlook leadership because:
- It is difficult to get authorization from IT
- Implementing new tools takes long processes
- SaaS tools are not purchased with user needs in mind
Overall, team members want to work more efficiently, and they need to do it as soon as possible.
Therefore, we recommend implementing mechanisms and protocols that facilitate IT’s intervention to authorize, propose, and implement new tools. Some examples include:
- Regular inter-team meetings
- Direct communication channels
- Regular SaaS audits
Control Your Onboarding & Offboarding Processes
As we previously mentioned, user access and permissions are crucial points of SaaS security. While it’s important for each new employee to have the required credentials to start working, it is equally essential that these credentials are accurate and provided within the appropriate timeframe.
It is also necessary to revoke the accounts of each departing employee. For this reason, part of the onboarding and offboarding processes must focus on these vital steps.
Choose the Right Vendor
Procurement teams shouldn’t select vendors lightly. They should perform thorough market research and look out for SaaS providers that:
- Have a good reputation
- Propose a committed partnership
- Is open for negotiation
- Comply with industry-specific requirements
Design a Recovery Plan
Even if you have not received a cyberattack, you should be prepared for one and have a recovery plan.
A good plan involves multiple steps:
- Impact assessment - Conducting a comprehensive evaluation of the attack's extent and consequences.
- Containment & mitigation - Taking measures to halt the attack's spread, minimize damage, and prevent future incidents. This may include disconnecting affected systems from the network, patching vulnerabilities, restoring clean backups, and implementing technical countermeasures.
- Communication and notification - Establishing a communication process to keep stakeholders informed.
- System and data recovery - Restoring compromised systems and data.
- Forensic analysis - Conducting a meticulous forensic analysis to determine the attack's origin, exploited vulnerabilities, and lessons learned.
- Enhancements and updates - Implementing improvements to the organization's security policies, procedures, and controls to enhance protection against future cyberattacks.
Implement Identity and Access Management
Identity and Access Management (IAM) is a set of practices, policies, and technologies used to manage and control user access to systems, applications, and resources in an organization.
Some of the most popular IAM mechanisms include:
- Two-factor authentication (2FA) or multi-factor authentication (MFA) - In addition to the password, a second authentication factor is requested, such as a code sent to the user's cell phone or a fingerprint.
- Certificate-based authentication systems - Each user is issued a certificate that verifies their identity when accessing the system or resource.
- Role-based access control (RBAC) - Users' access is based on their respective roles within the organization.
- Attribute-based access control (ABAC) - Users have access based on specific attributes, such as resource, action, and environment involved.
- Single Sign-On (SSO) - Users authenticate only once to access multiple systems or applications, with a central identity provider.
- Policy-based access control (PBAC) - This mechanism uses defined access policies to determine whether a user has permission to access specific resources.
Prefer Products with SOC 2 Type II certification
With the increasing adoption of cloud services, organizations place a lot of valuable information on third-party infrastructure. Ensuring that this data is well-protected from data breaches and security issues is vital for their business.
The best way to ensure compliance is to choose suppliers that are up to date with compliance requirements. Among the compliance requirements that a supplier can meet are SOC (System and Organization Control) reports.
The SOC framework's reports provide some of the best examples of efficient information security controls. There are three types of SOC reports that providers can offer, including:
- SOC 1 - Specifically designed for companies whose internal security controls may affect a user entity's financial reporting. It is specially focused on outsourced services.
- SOC 2 - this is a confidential report that demonstrates compliance with five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy.
- SOC 3 - This report is similar to SOC 2, but less specific and more general, SOC 3 is a report available to the public.
Additionally, there are two types of SOC 2 reports. They both evaluate a product’s safety, but there’s a fundamental difference when it comes to the evaluation period, compliance demands, and the cost of each report.
Vendors who meet SOC 2 Type I requirements evaluate their products for a limited timeframe and feature lower compliance requirements. On the other hand, obtaining SOC 2 Type II is more challenging due to its stringent compliance demands and higher costs.
Hence, we strongly advise selecting vendors with SOC 2 Type II certification. By doing so, you can ensure that your software providers adhere to rigorous safety standards and that they’re responsible for:
- Process monitoring
- Encryption management
- Intrusion detection
- User access authentication
- Disaster recovery
Use Encryption
Encryption is an essential component of SaaS security risk mitigation. It involves converting data into a format that can only be accessed by authorized parties with a decryption key.
You can use encryption to protect sensitive data within your SaaS tools and ensure secure transmission between the application and users.
Train Your Staff
End-user behavior plays a crucial role in SaaS security. Therefore, it is essential to provide training to all employees to ensure they adhere to SaaS norms and standards when using the applications. You can carry out the training in-house or ask the vendor to provide it.
Automate Operations
Most data breaches (95%) occur due to human error. Hence, automation is crucial to mitigating security risks. Therefore, we recommend you identify repetitive tasks and automate them to enhance their efficiency and security.
Apply Zero Trust Policies
Zero Trust is a security policy concept that assumes every user and device are insecure until proven otherwise. Incorporating the principle of Zero Trust into your organization's access policies could play a pivotal role in safeguarding your software environment.
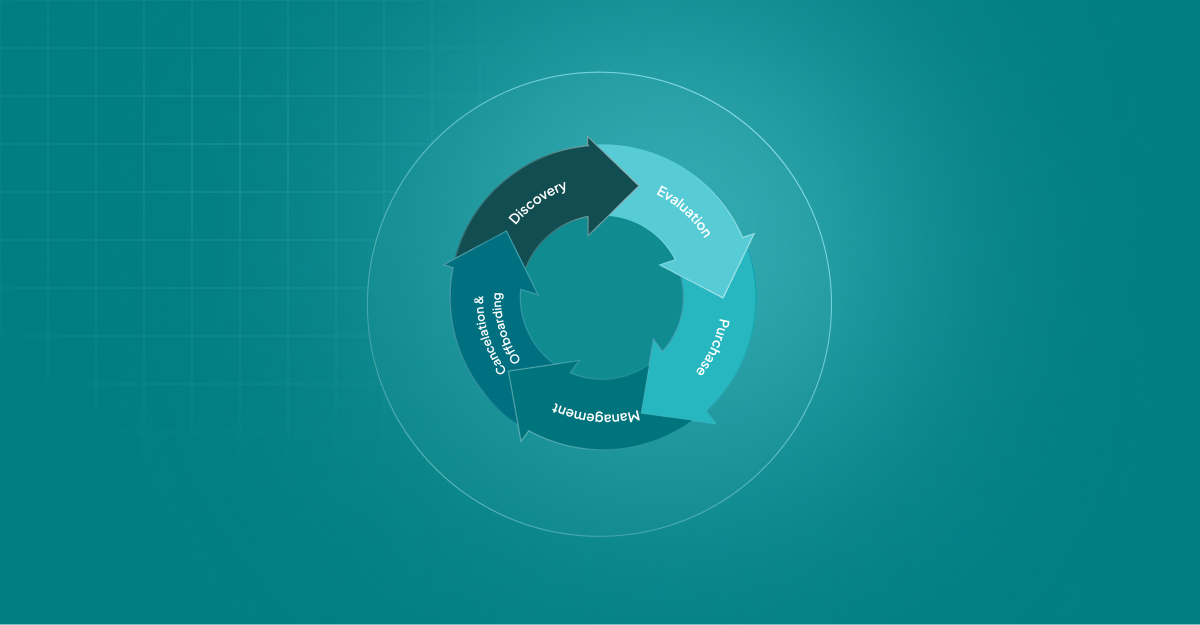
Maximize Your SaaS Stack's Security with Cledara**
Ensuring the security of your SaaS environment implies keeping a close eye on your SaaS stack. This requires time, effort, and dedication. Fortunately, Cledara makes SaaS management a breeze. Here’s where Cledara steps in.
Cledara is the only SaaS management platform that allows you to:
- Get a centralized view of all your SaaS subscriptions
- Avoid Shadow IT Control compliance
- Simplify onboarding and offboarding processes
- Check that all your suppliers have the right security measures in place
- Set an approval workflow for software purchases
- Seamlessly collaborate with Finance, IT, and Procurement teams
- Track user behavior
- Manage vendor relationships
Cledara is helping over 1,000 companies take control of their SaaS stack. Want to learn more? Book a demo today.
.webp)








.webp)
%2520(1).webp)
.webp)




.webp)